Question 1
Exhibit:
| RouterA#debug eigrp packets …… 01:39:13: EIGRP: Received HELLO on Serial0/0 nbr 10.1.2.2 01:39:13: AS 100, Flags 0x0, Seq 0/0 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/0 01:39:13: K-value mismatch |
A network administrator is troubleshooting an EIGRP connection between RouterA, IP address 10.1.2.1, and RouterB, IP address 10.1.2.2. Given the debug output on RouterA, which two statements are true? (Choose two)
A. RouterA received a hello packet with mismatched autonomous system numbers.
B. RouterA received a hello packet with mismatched hello timers.
C. RouterA received a hello packet with mismatched authentication parameters.
D. RouterA received a hello packet with mismatched metric-calculation mechanisms.
E. RouterA will form an adjacency with RouterB.
F. RouterA will not form an adjacency with RouterB.
B. RouterA received a hello packet with mismatched hello timers.
C. RouterA received a hello packet with mismatched authentication parameters.
D. RouterA received a hello packet with mismatched metric-calculation mechanisms.
E. RouterA will form an adjacency with RouterB.
F. RouterA will not form an adjacency with RouterB.
Answer: D F
Explanation
From the last line “K-value mismatch” we learn that the K values of two EIGRP routers are mismatched and EIGRP neighborship between two routers will not be formed.
Note: EIGRP K values are the metrics that EIGRP uses to calculate routes. Mismatched K values can prevent neighbor relationships from being established. By default K1 & K3 are set to 1 while K2, K4 and K5 are set to 0. We can change the EIGRP K values via the “metric weights tos k1 k2 k3 k4 k5” command under EIGRP router mode (tos: type of service must always be zero). For example:
Router(config-router)#metric weights 0 20 10 50 40 40
Question 2
When troubleshooting an EIGRP connectivity problem, you notice that two connected EIGRP routers are not becoming EIGRP neighbors. A ping between the two routers was successful. What is the next thing that should be checked?
A. Verify that the EIGRP hello and hold timers match exactly.
B. Verify that EIGRP broadcast packets are not being dropped between the two routers with the show ip EIGRP peer command.
C. Verify that EIGRP broadcast packets are not being dropped between the two routers with the show ip EIGRP traffic command.
D. Verify that EIGRP is enabled for the appropriate networks on the local and neighboring router.
B. Verify that EIGRP broadcast packets are not being dropped between the two routers with the show ip EIGRP peer command.
C. Verify that EIGRP broadcast packets are not being dropped between the two routers with the show ip EIGRP traffic command.
D. Verify that EIGRP is enabled for the appropriate networks on the local and neighboring router.
Answer: D
Explanation
The following list of parameters must match between EIGRP neighbors in order to successfully establish neighbor relationships:
+ Autonomous System number.
+ K-Values (look at the previous lesson).
+ If authentication is used both: the key number, the password, and the date/time the password is valid must match.
+ The neighbors must be on common subnet (all IGPs follow this rule).
+ K-Values (look at the previous lesson).
+ If authentication is used both: the key number, the password, and the date/time the password is valid must match.
+ The neighbors must be on common subnet (all IGPs follow this rule).
Therefore we don’t need to check EIGRP hello and hold timers because they don’t have to match. We should check if appropriate networks are included in the “network …” command of EIGRP on both routers.
Question 3
Refer to the exhibit.
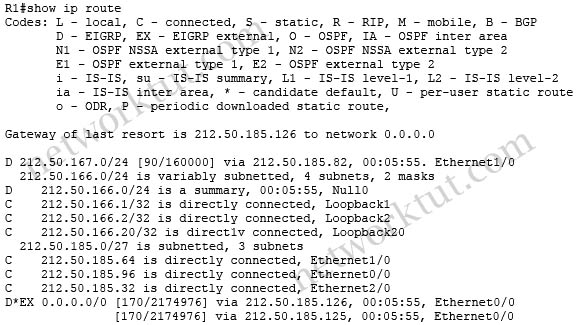
How would you confirm on R1 that load balancing is actually occurring on the default-network (0.0.0.0)?
A. Use ping and the show ip route command to confirm the timers for each default network resets to 0.
B. Load balancing does not occur over default networks; the second route will only be used for failover.
C. Use an extended ping along with repeated show ip route commands to confirm the gateway of last resort address toggles back and forth.
D. Use the traceroute command to an address that is not explicitly in the routing table.
B. Load balancing does not occur over default networks; the second route will only be used for failover.
C. Use an extended ping along with repeated show ip route commands to confirm the gateway of last resort address toggles back and forth.
D. Use the traceroute command to an address that is not explicitly in the routing table.
Answer: D
Explanation
For example in the topology below, R1 learned the Loopback0 interface of R6 via two equal paths R2-R4 and R3-R5:
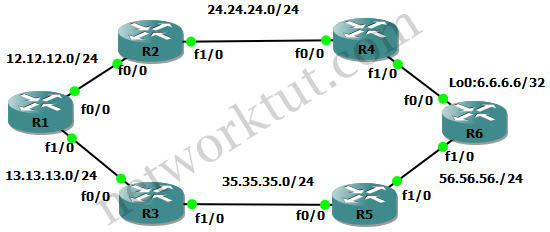
The routing table of R1 is shown below:
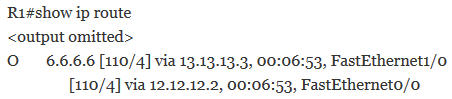
And the traceroute command from R1 to R6’s loopback0:
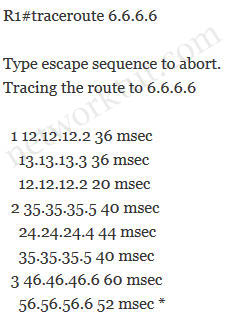
Traceroute works by sending packets with gradually increasing Time-To-Live (TTL) value, starting with TTL value of 1. The first router receives the packet, decrements the TTL value and drops the packet because it then has TTL value zero. The router sends an ICMP Time Exceeded message back to the source. The next set of packets are given a TTL value of 2, so the first router forwards the packets, but the second router drops them and replies with ICMP Time Exceeded. Proceeding in this way, traceroute uses the returned ICMP Time Exceeded messages to build a list of routers that packets traverse, until the destination is reached and returns an ICMP Echo Reply message.
The “1”, “2” and “3” in the traceroute output stands for the hop number. Therefore with the first hop (TTL is set to 1) we can see the packets are sent through 12.12.12.2 (R2) and 13.13.13.3 (R3). For the second hop (TTL is set to 2) they are 35.35.35.5 (R5) and 24.24.24.4 (R4)…
In conclusion we can use the traceroute command to check if the load-balancing is actually occurring.
Question 4
Which IPsec mode will encrypt a GRE tunnel to provide multiprotocol support and reduced overhead?
A. 3DES
B. multipoint GRE
C. tunnel
D. transport
B. multipoint GRE
C. tunnel
D. transport
Answer: D
Explanation
IPSec transport mode (encrypting an IP GRE tunnel) is a commonly deployed option because it provides all the advantages of using IP GRE, such as IP Multicast protocol support (and, thus, also the support of routing protocols that utilize IP Multicast) and multiprotocol support. Furthermore, this option saves 20 bytes per packet over IPSec tunnel mode (encrypting an IP GRE tunnel) because an additional IP header is not required.
Question 5
Which three features are benefits of using GRE tunnels in conjunction with IPsec for building site-to-site VPNs? (Choose three)
A. allows dynamic routing over the tunnel
B. supports multi-protocol (non-IP) traffic over the tunnel
C. reduces IPsec headers overhead since tunnel mode is used
D. simplifies the ACL used in the crypto map
E. uses Virtual Tunnel Interface (VTI) to simplify the IPsec VPN configuration
B. supports multi-protocol (non-IP) traffic over the tunnel
C. reduces IPsec headers overhead since tunnel mode is used
D. simplifies the ACL used in the crypto map
E. uses Virtual Tunnel Interface (VTI) to simplify the IPsec VPN configuration
Answer: A B D
Explanation
IPSec alone does not support multicast which many dynamic routing protocols use. GRE tunnels helps IPSec overcome this disadvantage by handling the transportation of multiprotocol and IP multicast traffic (from site-to-site VPNs, for example).
With the p2p GRE over IPsec solution, all traffic between sites is encapsulated in a p2p GRE packet before the encryption process, simplifying the access control list used in the crypto map statements. The crypto map statements need only one line permitting GRE (IP Protocol 47).
Reference:
Question 6
Which statement is true about an IPsec/GRE tunnel?
A. The GRE tunnel source and destination addresses are specified within the IPsec transform set.
B. An IPsec/GRE tunnel must use IPsec tunnel mode.
C. GRE encapsulation occurs before the IPsec encryption process.
D. Crypto map ACL is not needed to match which traffic will be protected.
B. An IPsec/GRE tunnel must use IPsec tunnel mode.
C. GRE encapsulation occurs before the IPsec encryption process.
D. Crypto map ACL is not needed to match which traffic will be protected.
Answer: C
Explanation
With the p2p GRE over IPsec solution, all traffic between sites is encapsulated in a p2p GRE packet before the encryption process, simplifying the access control list used in the crypto map statements.

0 comments:
Post a Comment